For defense manufacturers, supply chain accountability now extends past direct vendors and sub-tier suppliers, all the way to the fabrication source of every semiconductor in every component they field. Military OEMs are responsible for the entire genealogy of their supply chain, including sub-tier vendors their partners rely on but have never audited.
One adversarial semiconductor, one undisclosed firmware dependency, one documentation gap is all it takes to stall a project that’s otherwise ready to field.
Your HMI supplier sits squarely in that risk profile. Here’s what the mandates require and what to request from a partner who can actually help you meet them.

The U.S. Regulations Reshaping Defense Supply Chains
Two U.S. regulations are reshaping how defense OEMs evaluate their entire supply chain:
- NDAA Section 5949 (effective December 2027): Prohibits procuring electronics containing semiconductors from designated foreign entities. Compliance requires tracing the actual fabrication source of every semiconductor, not just the declared point of assembly.
- NDAA Section 889: Prohibits contracting with companies that use telecommunications or video surveillance equipment from named Chinese entities. Critically, suppliers must audit covered technologies potentially embedded in their own facilities, not just in the components they ship.
For programs with European exposure, SAFE and EDIP regulations impose similar adversarial content thresholds: capping third-country components at 35% and requiring a 65% minimum EU-origin content, respectively. The regulatory shift on both sides of the Atlantic closes the traceability gaps that allowed non-compliant content to go undetected in the first place.
What “No Adversarial Content” Actually Requires
A qualified HMI partner should be able to provide a “digital birth certificate” for every component, which is an unbroken, auditable trail covering:
- Semiconductor fabrication source (not just country of assembly)
- Material certifications for all metals, platings, and non-metallic compounds
- Firmware provenance and version control records
- AS9100-certified documentation of every manufacturing decision
- CMMC Level 2 validation confirming that all Controlled Unclassified Information is protected with the same rigor as design files

Vertically Integrated Manufacturing Gives You Visibility Where It Counts
The most direct defense against adversarial content isn’t a compliance checklist. It’s a supplier who controls their own manufacturing process under a single domestic roof.
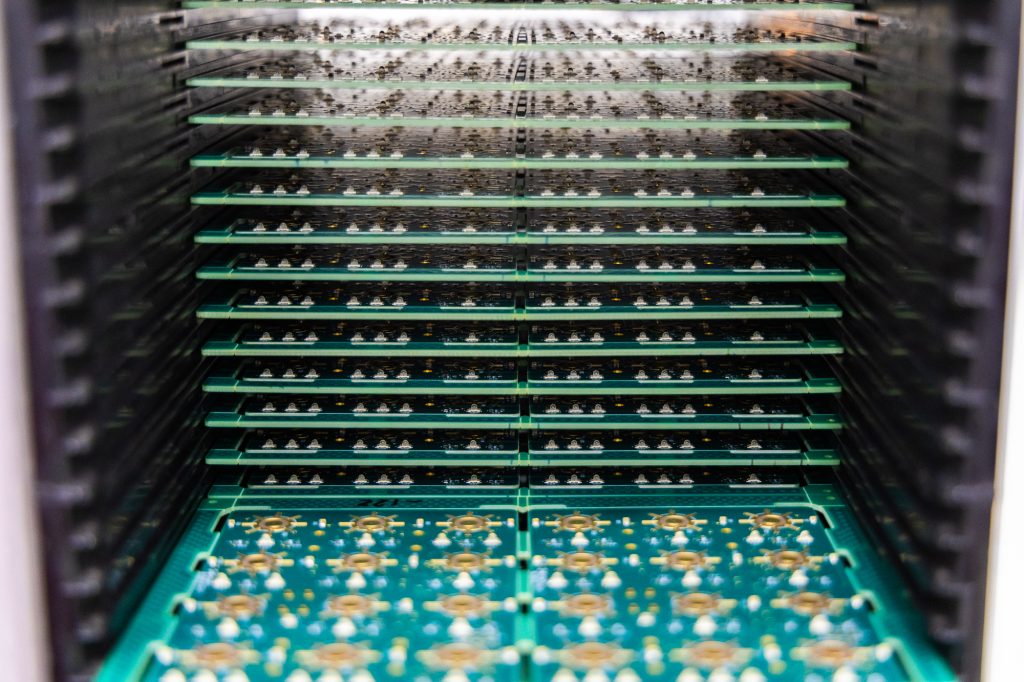
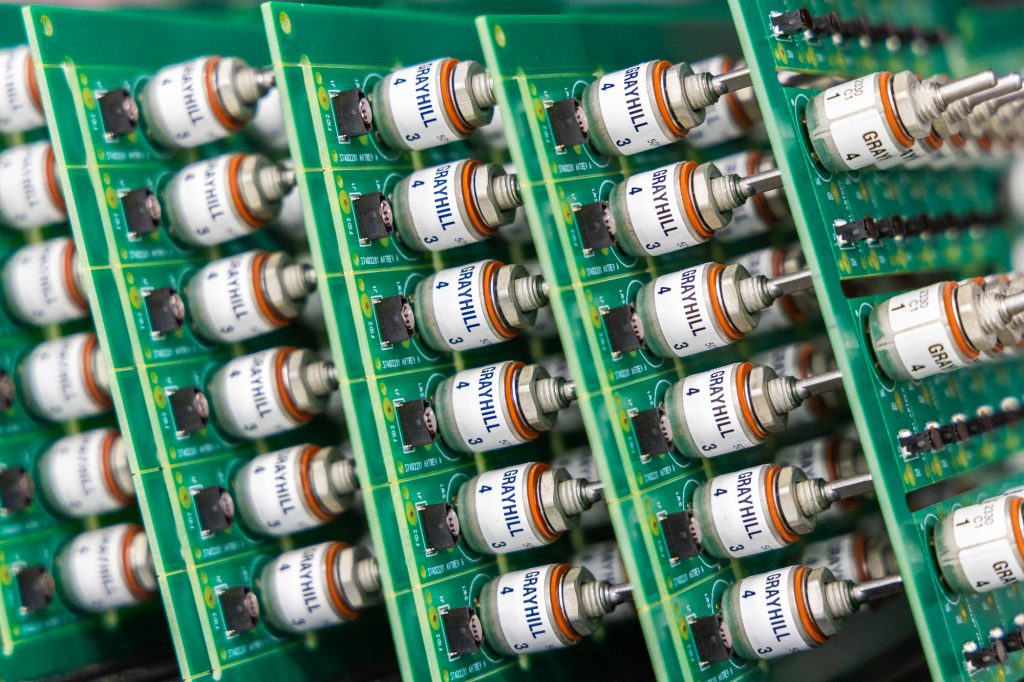
U.S.-based vertical integration in which the supplier owns the machine shop, plastic molding presses, PCB assembly lines, photometers for NVIS tuning, and 100% in-circuit test capability minimizes the sub-tier exposure that fragmented overseas supply chains create.
Questions to Ask Before You Qualify a Supplier
- Can they provide a written component genealogy tracing semiconductors to their source of fabrication?
- Where is your supplier manufacturing? Are they sourcing tools, software, and hardware domestically?
- What policies and controls do they have for protecting CUI across design files and manufacturing records?
The Bottom Line
Adversarial content risk doesn’t announce itself. It hides in sub-tier vendor relationships, undisclosed firmware dependencies, and semiconductor supply chains that look compliant at the finished-goods level. The right HMI partner doesn’t wait for a DCMA audit to find the gaps. They’ve already closed them—and they can prove it.
For a deeper dive into HMI supply chain compliance, download the complete HMI Supply Chain Handbook. This educational resource features:
- Environmental qualification standards
- Lifecycle management strategies
- Mission Readiness Checklist for evaluating suppliers



